Issue
-
How to make GitHub (and/or GitHub Enterprise) triggers Multibranch Pipeline in Jenkins.
Resolution
On Jenkins
A. Plugin Configuration
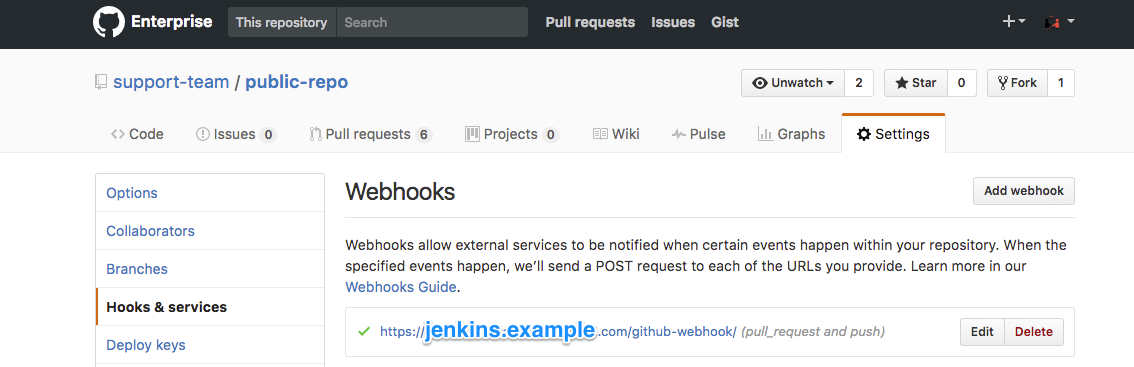
GitHub plugin as explained in GitHub Webhook configuration.
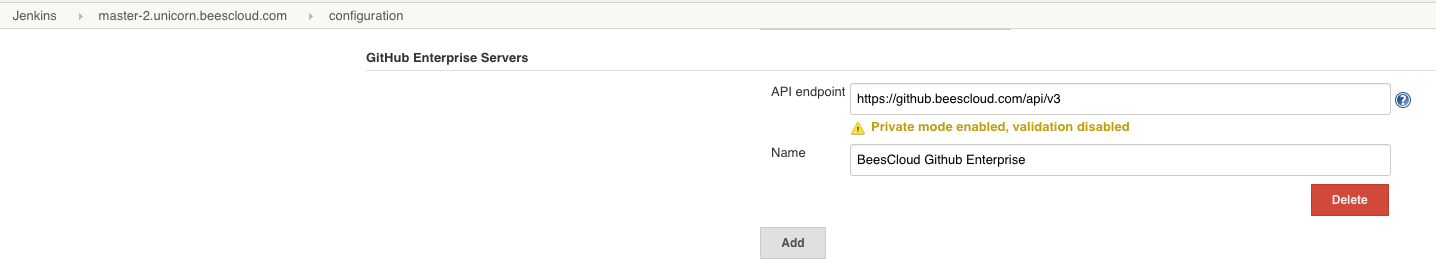
For GitHub Branch Source in case you wish to integrate with a GitHub Enterprise, it needs to be added in Manage Jenkins > Configure System > GitHub Enterprise Servers in order to fetch repositories from that endpoint.
B. Job Configuration
We are going to create a Multibranch Pipeline job/item which will scan the repository for creating a job for each branch found in the repository. You will need to follow these steps to create this Multibranch Pipeline:
-
Create a Multibranch Pipeline and go into its configuration.
-
Add a source in
Branch Sourcessection selecting a GitHub option. -
For Credential use
Username and Password, typing as password the personal access token. Note: ThisCredentialsfield is required only if you want to provide a private repository. -
Choose one of the two method for specifying the repository:
Repository HTTPS URLandRepository Scan.
Repository HTTPS URL
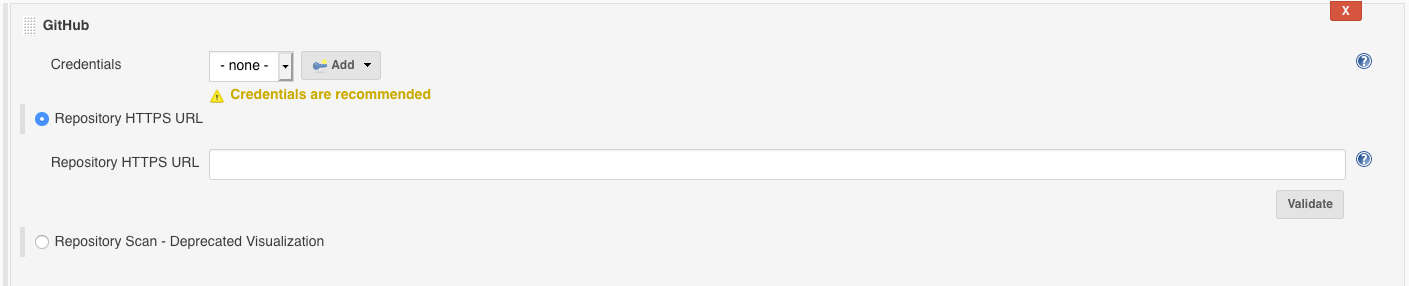
This is the default and recommended method. Here, you will put the repository URL in the Repository HTTPS URL field.
You can use the Validate button to check if your Jenkins instance has access to the provided URL.
Repository Scan
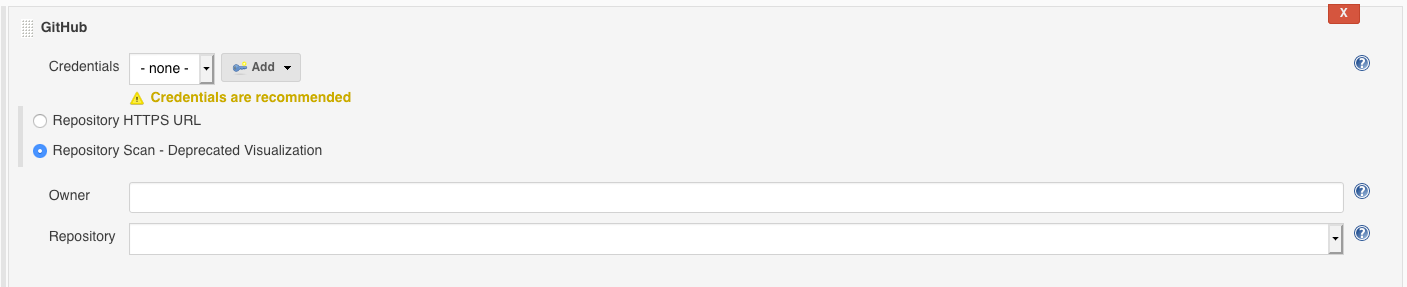
This method is deprecated for performance reasons. You could want to use it if you don’t know the repository URL but you know the account owner of the repository. To use this method you will need to follow the following steps:
-
Select
Respository Scan - Deprecated Visualization. -
For
Owneruse the GitHub user/organization. -
Select on of the fetched
Repositoryfrom theOwner.
For both method (Repository HTTPS URL and Repository Scan) and if you are using SCM API 2.2.4 or higher, please check the Behaviors section and ensure Filter by name is removed unless you only want to discover a subset of branches. If it is configured, please recall to include PR-* to Discover Pull Requests.
Suppress Automatic SCM trigger propertyIt disables any automatic triggering, not only coming from push / pull request / repository notification but also from branch indexing. |
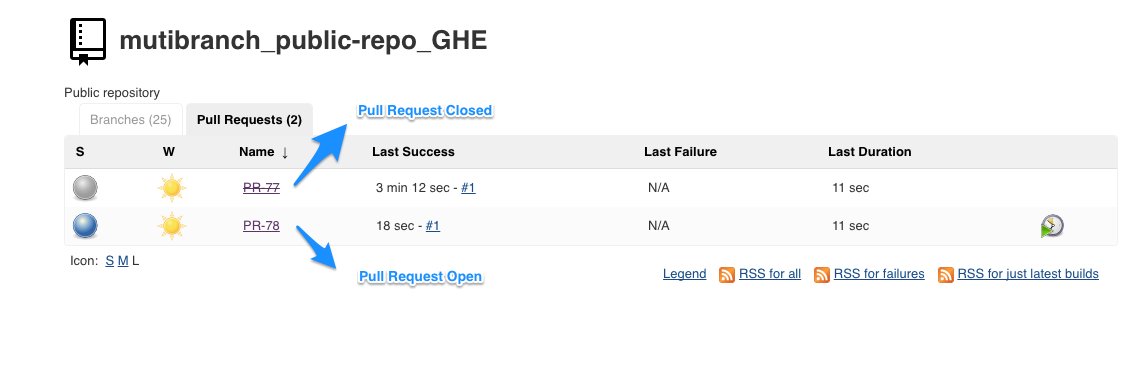
After saving the job, two views area created: one for Branches (Push events) and another for Pull Request.
Troubleshooting
If the post-receive hooks are not there, please review Troubleshooting
Tested products/plugins version
The latest update of this article has been tested with:
-
CloudBees CI on traditional platforms - Client controller 2.387.1.2
-
GitHub plugin 1.37.0
-
GitHub Branch Source Plugin 1701.v00cc8184df93