Issue
I’d like to configure a simple RBAC setup with:
-
administrators able to control all the cluster.
-
developers who could see the Operation Center items and have the rights to manage jobs on their controller.
Environment
-
CloudBees CI (CloudBees Core) on modern cloud platforms - Managed controller
-
CloudBees CI (CloudBees Core) on modern cloud platforms - Operations Center
-
CloudBees CI (CloudBees Core) on traditional platforms - Client controller
-
CloudBees CI (CloudBees Core) on traditional platforms - Operations Center
-
CloudBees Jenkins Enterprise
-
CloudBees Jenkins Enterprise - Managed controller
-
CloudBees Jenkins Enterprise - Operations center
Resolution
Setting up the roles
-
administer role which has the rights to do anything
-
developer role which has the rights to create, read and configure items
-
browse role which has the rights to read items, and the overall read right
Let’s start by configuring those roles, going to <cjoc>/plugin/nectar-rbac/manage/,
you’ll find a matrix, add the three roles and then select the permissions for each roles.
You should end up with something like this:
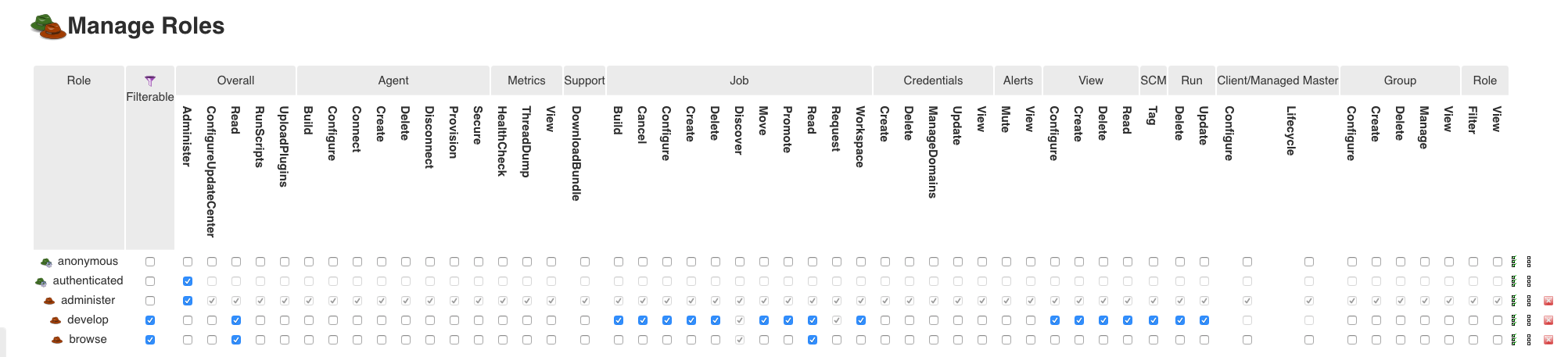
3 important notes:
-
the administer role should NOT be filterable. Filterable means that the role can be removed on a sub container (eg a folder or a Managed controller). We want an admin to be admin anywhere on the cluster.
-
the authenticated role is still able to do anything, this is really important not to lock yourself out.
-
make sure to read all the permission description, you might want to have more granularity than the one of this example.
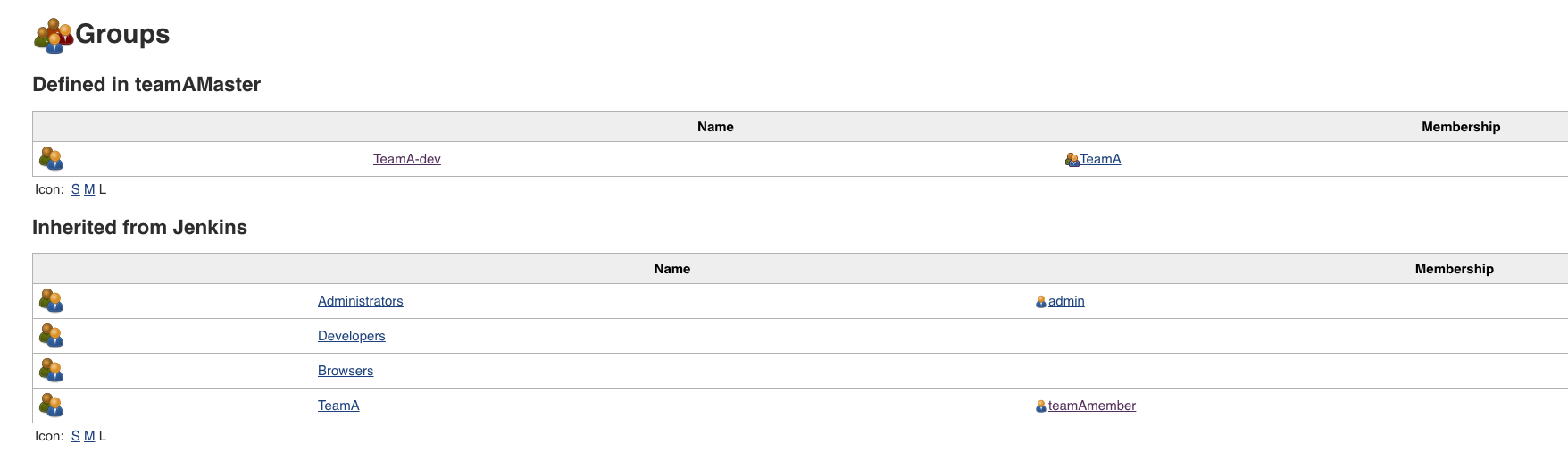
Setting up the groups at the Operation Center Level
We will then create two groups:
-
Administrators: that will be able to administer all the cluster
-
TeamA: the members of teamA
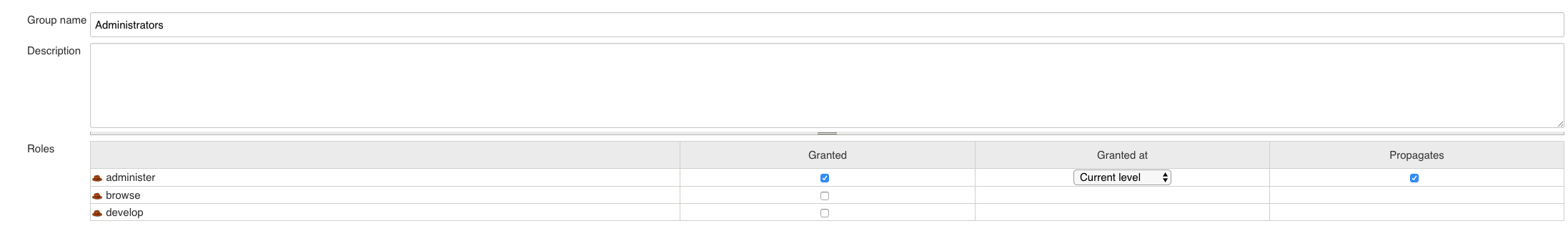
Let’s do it, going to <cjoc>/groups/, click on the New Group on the left column, create the Administrators group, and grant the group the administer role:
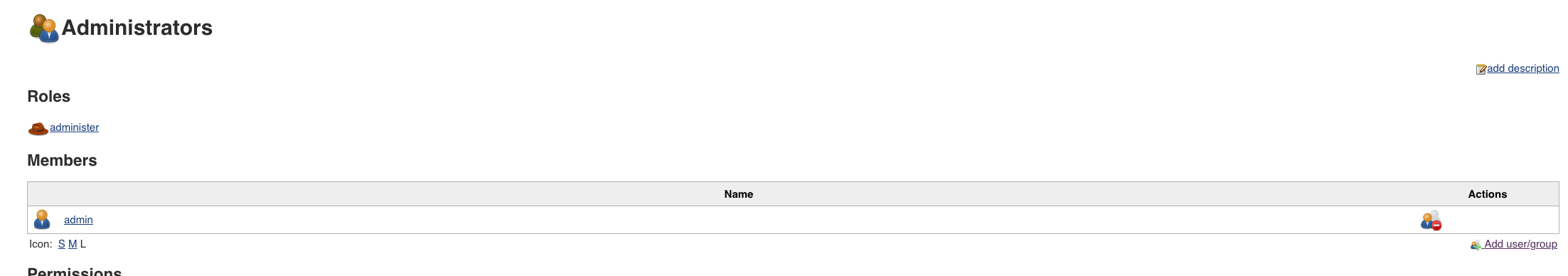
Save and click on Add user/groups to add the admins to the group. In this case I only added the admin user:
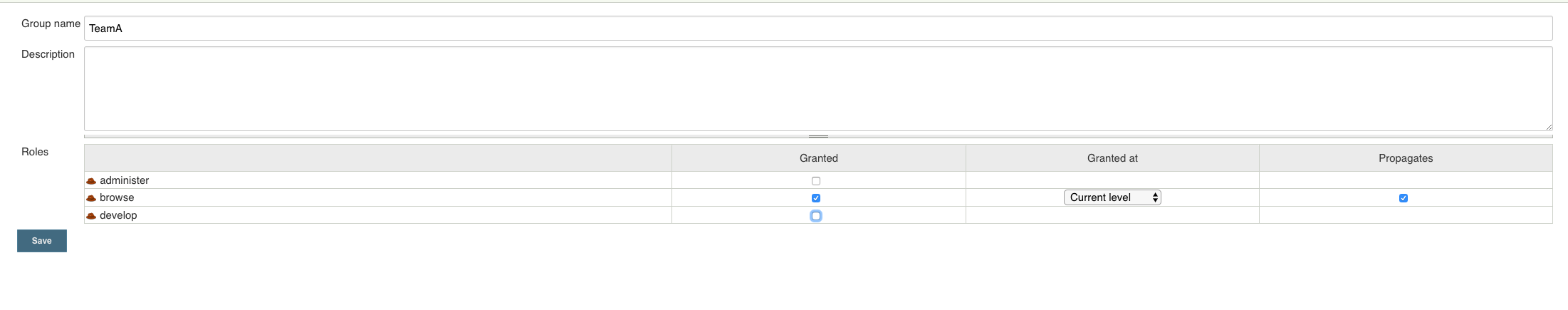
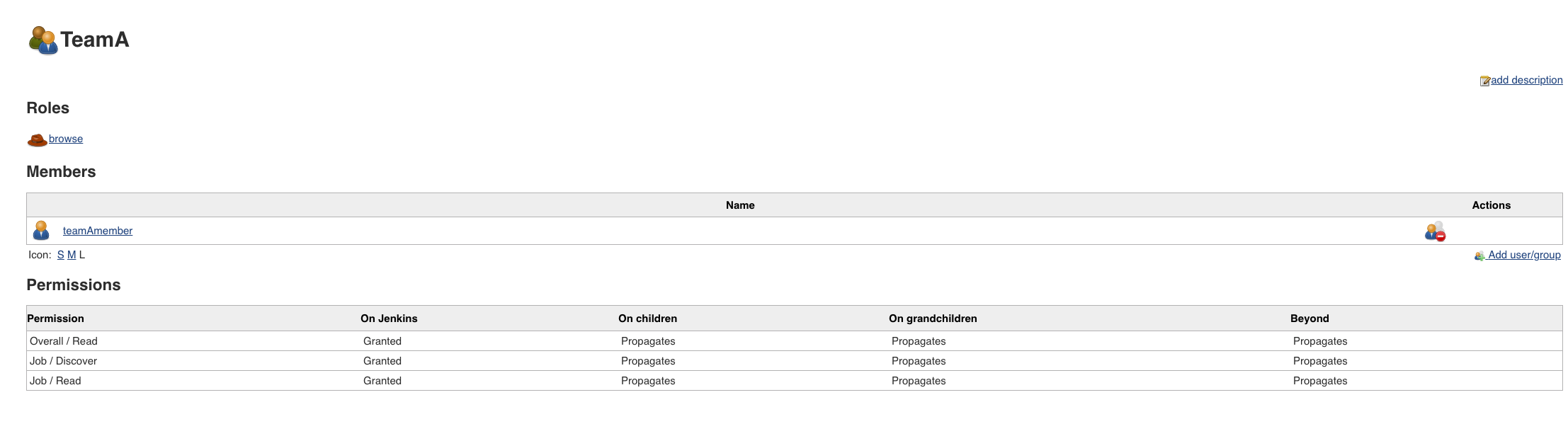
We will then do the same for the TeamA, create a new group and grant it the browse role:
Setting up the developer group at the controller level
Currently we successfully defined:
-
an admin group that can do anything on the cluster.
-
a group for the developer of the teamA that have read only rights on the cluster.
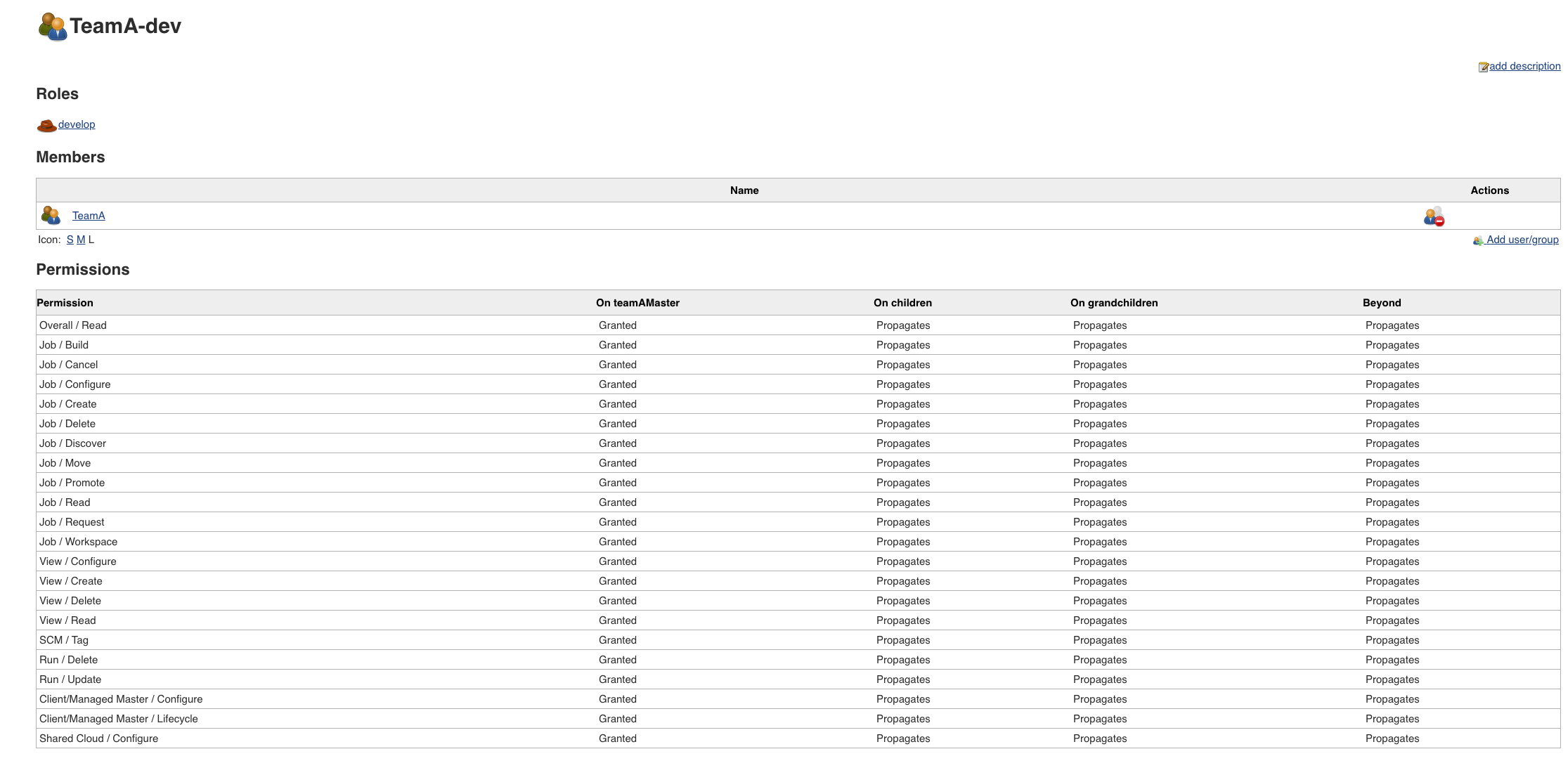
We now want our developers to be able to create items on the teamAcontroller. We will therefore create a new group, at the level of the controller to grant the developer role to the teamA members on the controller.
Go to <cjoc>/job/teamAMaster/groups/ and create a new group, that we will call TeamA-dev, grant it the developer role and add the TeamA group as member of this group.
You should end up with something similar to those screenshots:
Removing the Authenticated role any permission
At this point, the setup should be ready. We can now remove the Authenticated user any access.
For this double check that at least you are added to the Administrators group, then go back to <cjoc>/plugin/nectar-rbac/manage/ and remove any permission to authenticated.
Conclusion
As we saw, the RBAC setup is flexible. Before going into a more complex implementation, you will need to draw a map of the users, groups and roles that you will need. The RBAC feature not only works with Client/Managed controllers, but with a lot of different Jenkins items, like the folders. Principle is always the same.
The CloudBees Jenkins Platform - Admin training can give you more insights on the RBAC feature.