Symptoms
-
The log-in process is very slow
-
Jenkins takes too much time to recognize the AD groups
-
I am able to log-in on Jenkins
-
AD groups are recognized by Jenkins
-
In /whoAmI AD groups appear
Diagnosis/Treatment
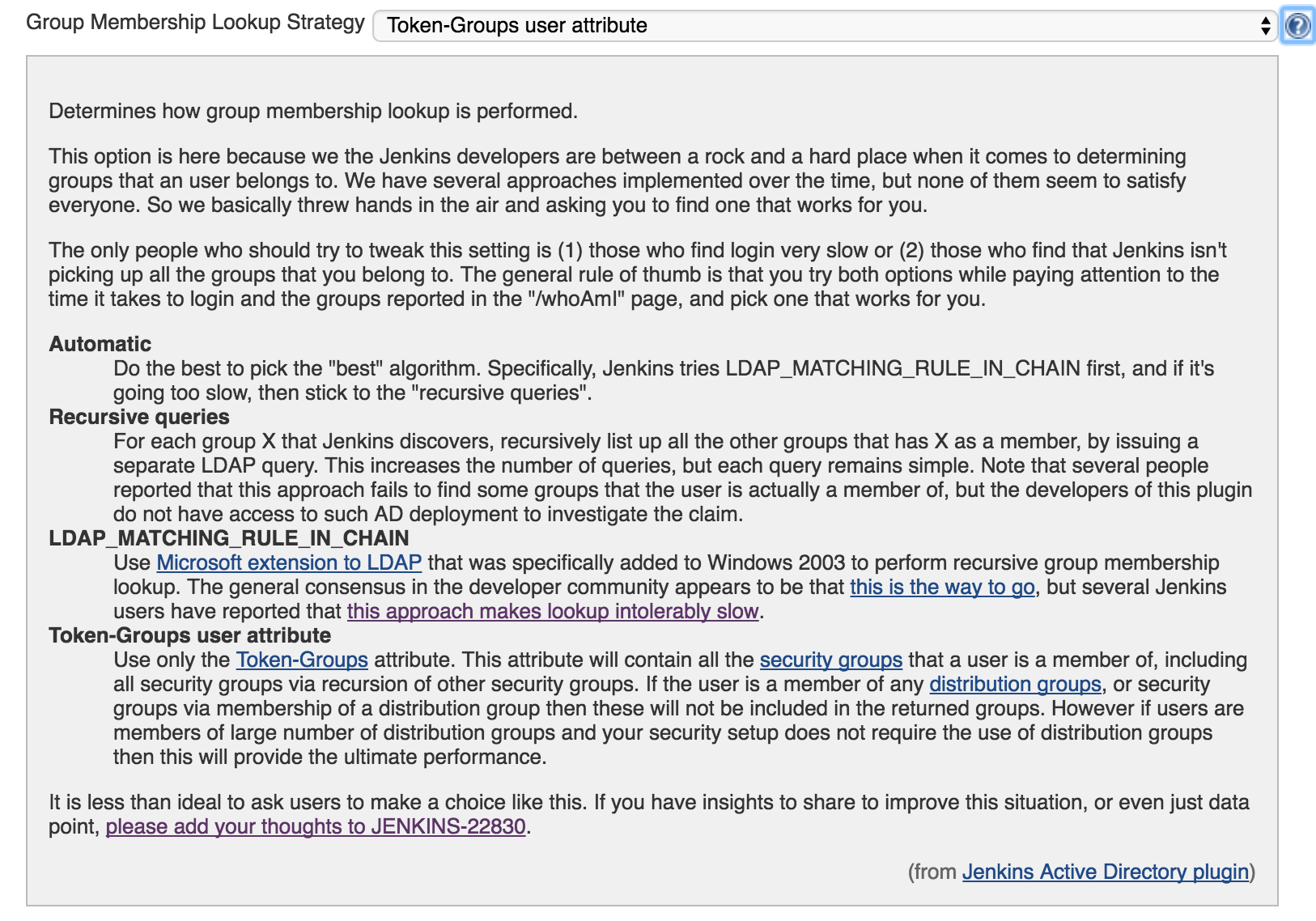
Try with Token-Groups user attribute
Unfortunately, for the moment the AD plugin does not allow you to restrict Groups lookup on the same way you can do it with the LDAP plugin.
On the other hand, in case your AD set-up only relies on Security Groups, and not Distribution Groups - in which in most of the cases it happens- then you can try to use Group Membership Strategy → Token-Groups user attribute. This might improve the login performance as we are reducing the scope of the querry launched agains the AD server.
Use the global catalog
By default, in case you don’t specify any Domain Controller in the plugin configuration, the plugin will check if your AD domain is exposing any Global Catalog, if this is the case, the plugin will perform the lookup on the Global Catalog port (3268/3269). The LDAP catalog (389/686) might be much more slower than the Global Catalog since in order to retrieve the user information several LDAP servers might need to talk between them.
To discover if your AD server is exposing the LDAP vs Global Catalog, you can launch the request below from your Unix terminal.
nslookup -q=SRV _ldap._tcp.<DOMAIN_NAME> nslookup -q=SRV _gc._tcp.<DOMAIN_NAME>
CloudBees Support Team recommends the Global Catalog.
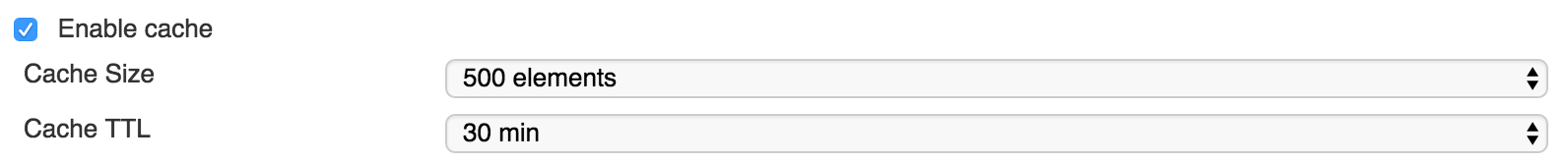
Enable the cache
This is one of the options which might increase the performance of your Jenkins instance when there are consecutive lookups. Enabling this option is strongly recommended.
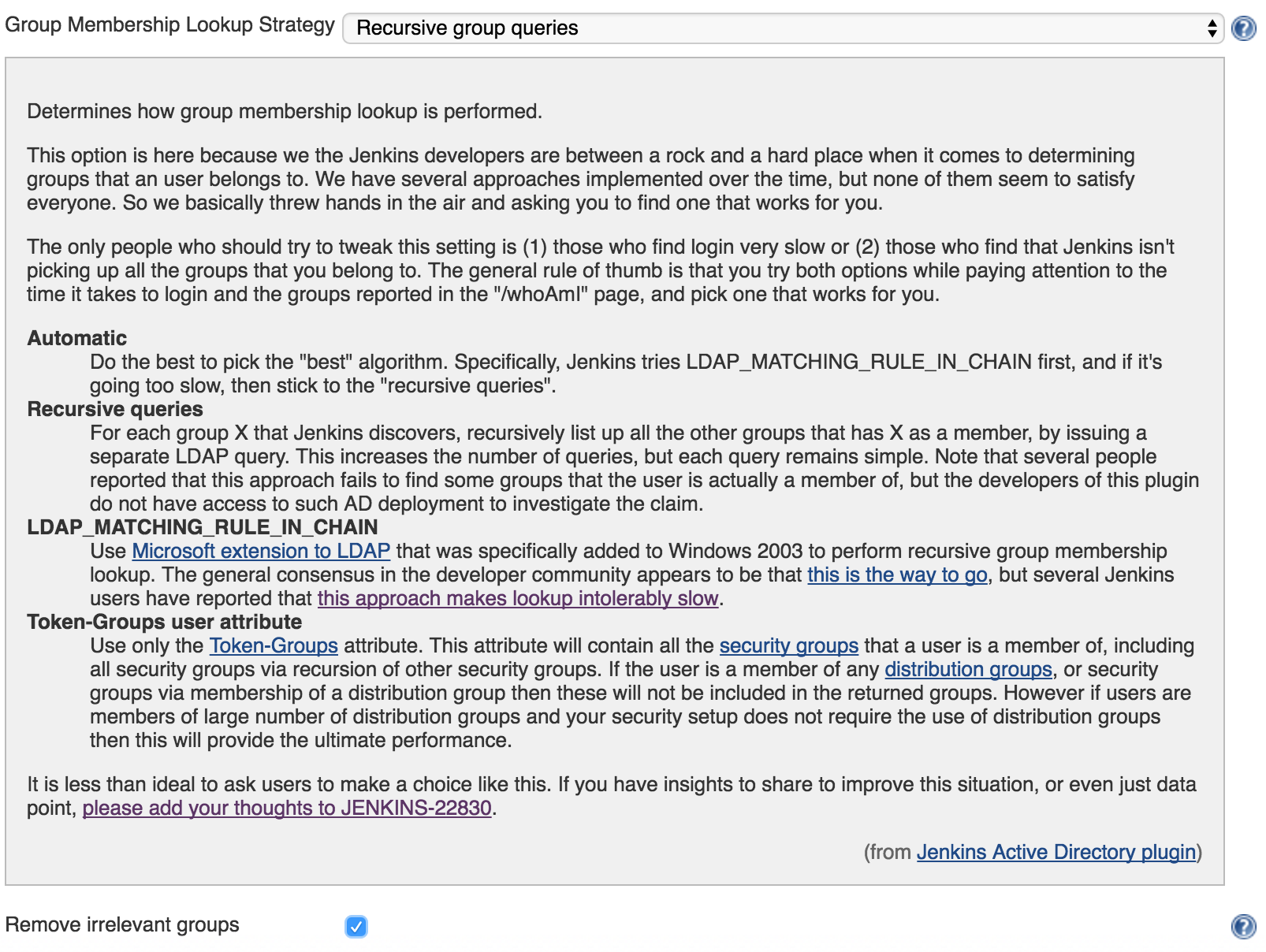
Try removing irrelevant groups with the Recursive group queries
Makes Jenkins ignore every user’s Active Directory groups that are not being used by the active Authorization Strategy. This can significantly improve performance in environments with a large number of groups but a small number of corresponding rules defined by the Authorization Strategy.
-
IMPORTANT: This setting may be incompatible with some Authorization Strategies. For example, it has been reported that this setting can impact RBAC strategy by modifying the defined privileges for certain users (e.g. some permissions are missing).