Use this action to scan repositories for dependency vulnerabilities with the Black Duck Software Composition Analysis (SCA) scanner, and then view comprehensive security results in CloudBees Unify. You can also use the action output as a quality gate for the next step or job in your workflow.
This action is available on the GitHub marketplace.
Black Duck is a software composition analysis (SCA) scanning solution that helps organizations manage risks associated with open-source software in terms of security, license compliance, and code quality.
Add a Black Duck scan to your workflows in CloudBees Unify to:
-
Detect open-source and third-party dependencies in software, source code, and artifacts with multiple analysis techniques.
-
Identify code vulnerabilities and receive timely security advisories.
-
Gain insight into security risks and how to fix vulnerabilities.
CloudBees Unify enables you to run a Black Duck scan either implicitly or explicitly.
Explicit and implicit scan types
An implicit scan is automatically triggered, and an explicit scan is one you configure to be invoked in a step of your workflow. To learn more about the differences between explicit and implicit scans, refer to CloudBees actions.
To set up implicit scanning, refer to Code and binary security analysis.
Prerequisites
Set up CloudBees Unify and GHA to work together, providing key features of CloudBees Unify to GHA workflows. Refer to Getting started for more information.
How the scanner works
The Black Duck SCA scanner architectural components are:
-
Client-side: The Black Duck Detect scanning tool, the Signature Scanner command-line tool, and the REST API.
-
Server-side: The Black Duck server.
-
Data center: The Black Duck KnowledgeBase open-source software database.
The scanning process is as follows:
-
The Black Duck Detect tool is used to authenticate and initiate the code scan.
-
Codebases are scanned on the client side.
-
The scan data is uploaded to the Black Duck server with the Detect tool. The completed scan data does not contain any source code, to maintain your code security. The completed scan contains only file and directory signatures, and information derived from package management files.
-
The scan data is sent to the Black Duck KnowledgeBase, and open-source components in your code are matched and identified. The matching/identification process is based on your package manager data and SHA1 hashes created by the Signature Scanner when it scans your files and directories.
-
The REST API is used to fetch the bearer token and retrieve the scanning results.
-
The matched open-source components are reported as a viewable Bill of Materials that contains the associated security, licensing, and operational risks of the discovered components.
| For more information about the Black Duck SCA scanner, refer to the Black Duck documentation. |
Inputs
| Input name | Data type | Required? | Description |
|---|---|---|---|
|
String |
Yes |
The Black Duck client secret. |
|
String |
Yes |
The Black Duck server URL. |
|
String |
No |
The CloudBees Unify URL.
The default value is |
|
String |
No |
Specify any Black Duck Detect properties. |
|
String |
No |
The Black Duck project name. |
|
String |
No |
The Black Duck project version. |
Outputs
| Output name | Data type | Description |
|---|---|---|
|
String |
The number of Critical security findings discovered during the scan. |
|
String |
The number of Very high security findings discovered during the scan. |
|
String |
The number of High security findings discovered during the scan. |
|
String |
The number of Medium security findings discovered during the scan. |
|
String |
The number of Low security findings discovered during the scan. |
This action uses GitHub OIDC authentication to securely communicate with CloudBees Unify. Be sure to set permissions to id-token: write in your workflow.
|
Usage examples
The following is a basic example of using this action:
permissions: id-token: write contents: read steps: - name: Scan with Black Duck SCA uses: cloudbees-io-gha/blackduck-scan-publish@v2 with: api-token: ${{ secrets.BLACK_DUCK_TOKEN }} server-url: ${{ vars.BLACK_DUCK_URL }}
In the following example, the Black Duck Detect properties
logging.level.detect and blackduck.offline.mode are specified:
Using the action output
You can use the output values from this action in downstream steps and jobs. The following example uses the action output in a downstream step of the same job:
The following example uses the action output in a downstream job:
Full workflow and run example
The following GHA workflow example scans a repository with Black Duck.
Example GHA workflow YAML file
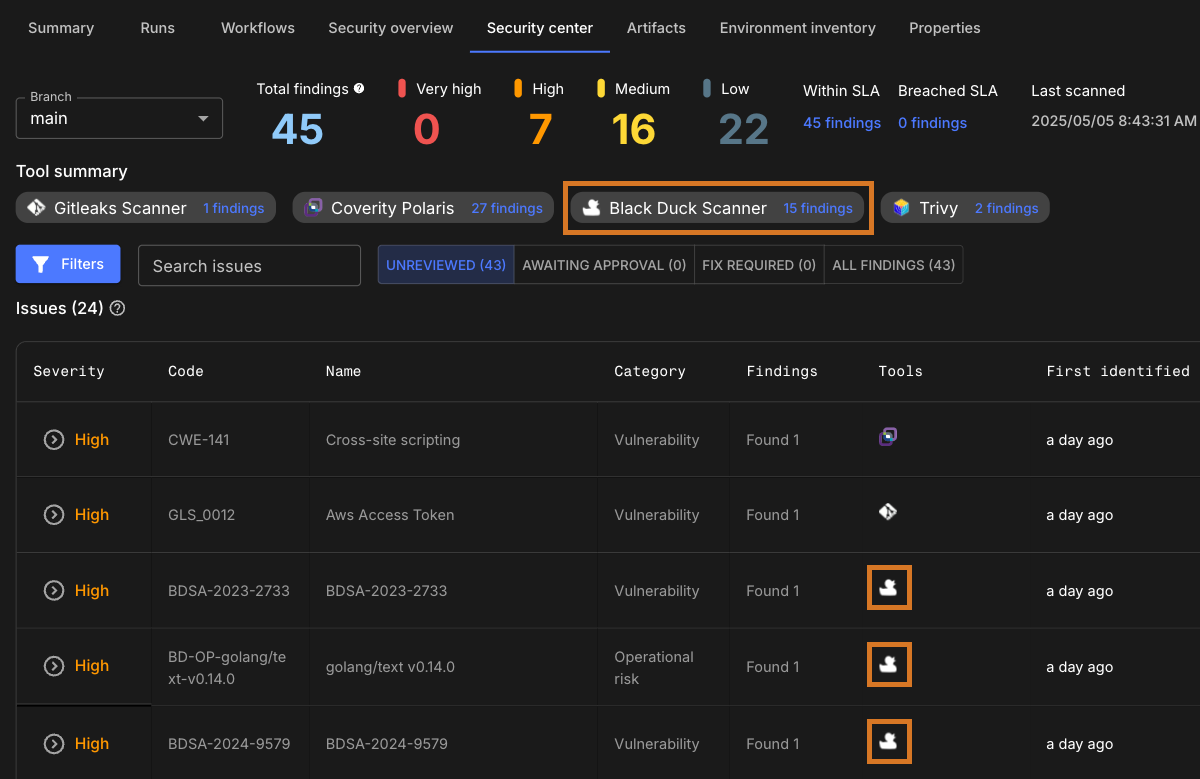
After the GHA run has completed, the security findings are collected and displayed in the Component security center of the component containing the workflow.
Scan a CloudBees Unify workflow explicitly with Black Duck
If you are using a CloudBees Unify workflow rather than a GHA workflow, explicitly scan with the CloudBees Black Duck action.