This section provides an overview of deploying CloudBees CD/RO within Kubernetes. It summarizes the benefits and provides an overview of how CloudBees CD/RO components are configured.
Clustered CloudBees CD/RO in Kubernetes
Clustering CloudBees CD/RO in Kubernetes provides several advantages, such as:
-
Helping to ensure high-availability.
-
Expanding your platform’s long-term capacity through easy scaling.
-
Increasing the number of simultaneous jobs and API requests your platform can support and distributing them across multiple CloudBees CD/RO servers and web servers.
| Before committing your resources to a full production environment, you can also install the CloudBees CD/RO Kubernetes demo. |
Within the Kubernetes environment, Helm charts are the primary method to configure CloudBees CD/RO components. From configuring your license information and database connections to autoscaling and platform specific implementation, these charts provide a central location to configure nearly all aspects of CloudBees CD/RO installations.
The following diagram depicts CloudBees CD/RO and an additional agent running as services in a production environment within a Kubernetes namespace.
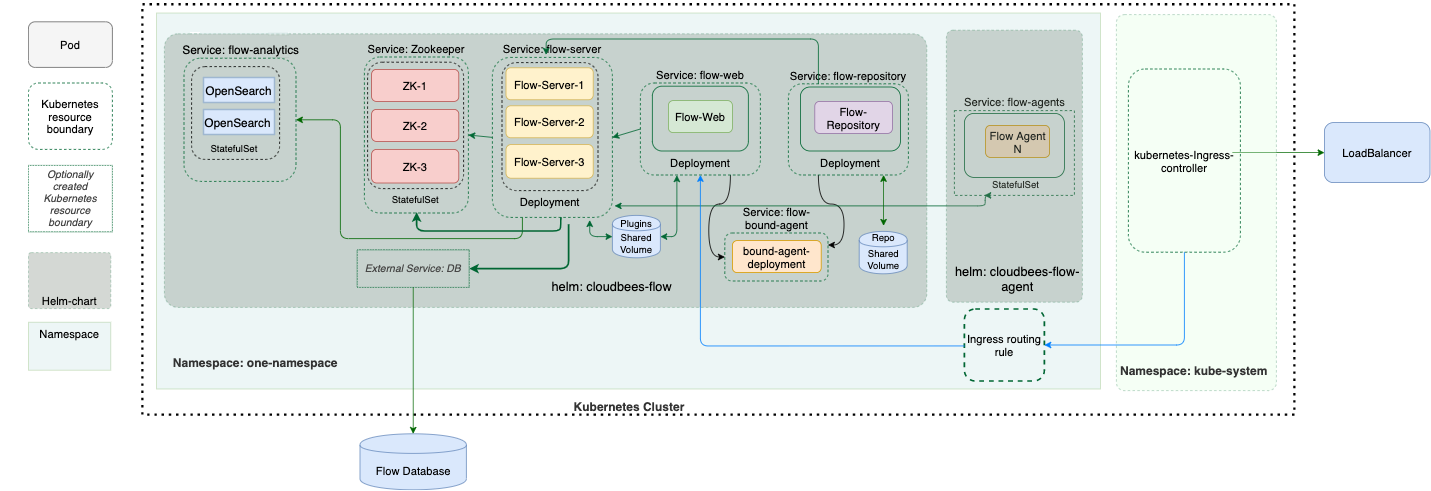
These components are configured from two Helm charts:
-
The
cloudbees-flowchart provides the configurations for the following components:-
CloudBees CD/RO server (
flow-server) -
CloudBees CD/RO web server (
flow-web) -
CloudBees Analytics server (
flow-analytics) -
The repository server (
flow-repository) -
A bound agent (
flow-bound-agent), which serves as a local agent for the CloudBees CD/RO and repository servers.Bound agents are internal CloudBees CD/RO componentsThe CloudBees CD/RO bound agent (
flow-bound-agent) is an internal component used specifically by CloudBees CD/RO for internal operations. While it is possible to schedule user jobs on bound agents, they are not intended for this purpose, and CloudBees CD/RO agents should be used instead.If operations other than CloudBees CD/RO internal operations run bound agents, CloudBees CD/RO performance may become unpredictable. Additionally, system requirements for CloudBees CD/RO instances assume that bound agents are used exclusively by CloudBees CD/RO, and are not reliable for instances where user jobs are also running.
-
Zookeeper
-
Ingress NGINX Controller
-
Shared volumes for plugins and repositories
An external database must be installed in CloudBees CD/RO production environments, which requires an enterprise license. To avoid installation errors, your CloudBees CD/RO server licence and database connections should be configured in the cloudbees-flowchart prior to installation. -
-
The
cloudbees-flow-agentchart provides configuration for one or more agents (flow-agent) to execute commands, monitor statuses, and collect results, all in parallel across pods. Each agent can be configured independently to provide specific resources for the tasks it executes.
Examples of these charts with default values are available publically and may be adapted to fit the needs of your production environment.
Next steps
To watch a demo installation, install the demo, or install a production environment, refer to Install CloudBees CD/RO within Kubernetes.
To get started customizing Helm charts for your Kubernetes environment, refer to Configure Helm charts.